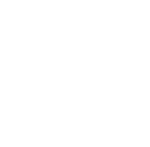
If you’re a Telegram user like me, you may have experienced extremely slow connection speeds or no connection over the weekend. This was because Telegram’s Asia Pacific cluster was under DDoS attack since Friday morning.
South East Asia, Oceania, Australia and some parts of India were affected. The downtime affected 5% of its entire global user base and 30% in Asia.
Telegram reported that they were hit with 200Gbps of junk traffic, which it described as “feels roughly like having 200 billion very random people squeeze into your bus every second.”
The junk traffic was said to have originated from thousands of infected servers, and distributed evenly across thousands of hosts. None contributed more than 5% of total volume.
What’s DDoS, you ask? Distributed Denial-of-Service is a form of attack that uses a network of compromised computers (usually via malware, trojans) labeled ‘botnet’ to overwhelm resources and bandwidth of servers and networks. One of the ways is sending a massive amount of ‘little packets’ of junk traffic to overwhelm servers, inundating them. This usually causes servers to slowdown or crash completely.
It may sound crazy, but you can ‘buy’ a DDoS attack on the black market for as little as US$150.

The Telegram team claims it hasn’t experienced a DDoS attack of this scale before, and explained that this is a relatively new type of DDoS method known as Tsunami SYN Flood. The last massive DDoS was in late September 2014, in the height of the South Korean privacy scandal.
While mitigating a DDoS attack is tricky (as it’s not easy to determine what is garbage traffic and which legitimate), Telegram has identified the attack as “being coordinated from East Asia.”
It noticed a three-fold increase in signups from South Korea in the last two weeks.
If you aren’t aware, LINE filed a complaint to Google regarding Telegram’s use of custom stickers in its Android app. Google subsequently removed Telegram from the Play Store, only to return it hours later. Telegram believes however, it is highly unlikely the Korean messaging company coordinated the DDoS attack itself.
The other theory points to China, as Telegram has picked up some notoriety for its self-destructive messaging feature. The service was labeled an “anti-government” tool in China’s Peoples Daily newspaper, as it was reportedly used by human rights lawyers who were arrested by the government last Friday.
Telegram founder Pavel Durov told TechCrunch, “We know nothing for sure, so we do no make any accusations.” He continued, “One thing is certain: somebody powerful in Asia is unhappy. We have never seen DDoS of such scale and efficiency before. And we’ve seen a lot.”
China has a ‘colourful’ history with messaging apps and social media platforms. LINE and Kakao Talk were blocked in China last year on suspicion of helping “spread information linked to terrorists activities.” Many of consumers’ most loved social tools and web services like Facebook, Twitter, Instagram and Google are also blocked in China. Under China’s iron-fisted internet censorship policy over 2,700 websites are currently or were blocked.
It was reported that Telegram was also getting blocked, over the lawyer controversy.
That being said, orchestrating a DDoS attack is a criminal offence in most countries so attackers hide their tracers as best they can. Could it be an angry government? Or a jealous competitor?
In the latest Akamai State of Internet report, Q1 2015 set a record for the number of DDoS attacks, more than double recorded in Q4 2015. The trend points to lower bandwidth paired with longer attack campaigns. Another form of attack taking advantage of the Simple Service Discovery Protocol (SSDP) accounted for more than 20% of attacks. Read more about the Q1 2015 State of the Internet – Security Report from Akamai.
It looks like everything is up and running smoothly at the moment. Telegram has assured that its ‘sysadmin cyborgs’ are working round the clock to make sure everything runs flawlessly for 100% of its users.