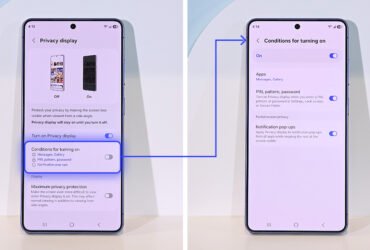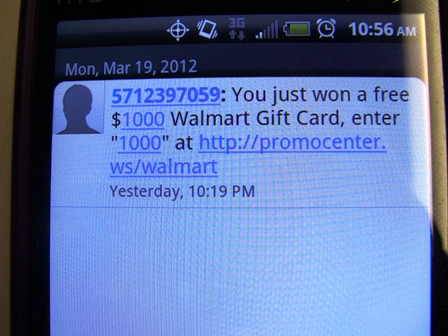
Researchers from North Carolina State University recently published a video demonstrating how a mobile app can simulate the reception of a SMS message from a spoofed source. In a blog post on Symantec’s official blog, Symantec reportedly found SMS spoofing codes in 200 apps found on Google Play Store, with millions of combined downloads.
SMS spoofing can be used for numerous malicious intentions, including SMS phishing attacks (Smishing). Much like web phishing, the intent is usually to trick someone into revealing banking credentials or subscribing to paid services.
Symantec has not found any instances that use the spoofing code for a malicious SMSishing attack to date. It found that the principle reason to use such codes in apps is to push advertisements.
Symantec advises users to be wary of the source of any suspicious incoming text messages while Google makes changes to Android to prevent SMS spoofing. These applications may be identified by Norton Spot and any future malicious usage are detected by Norton Mobile Security.
Catch the video below:
Catch full details of the demonstration.
[ad#Google Adsense 336×280]