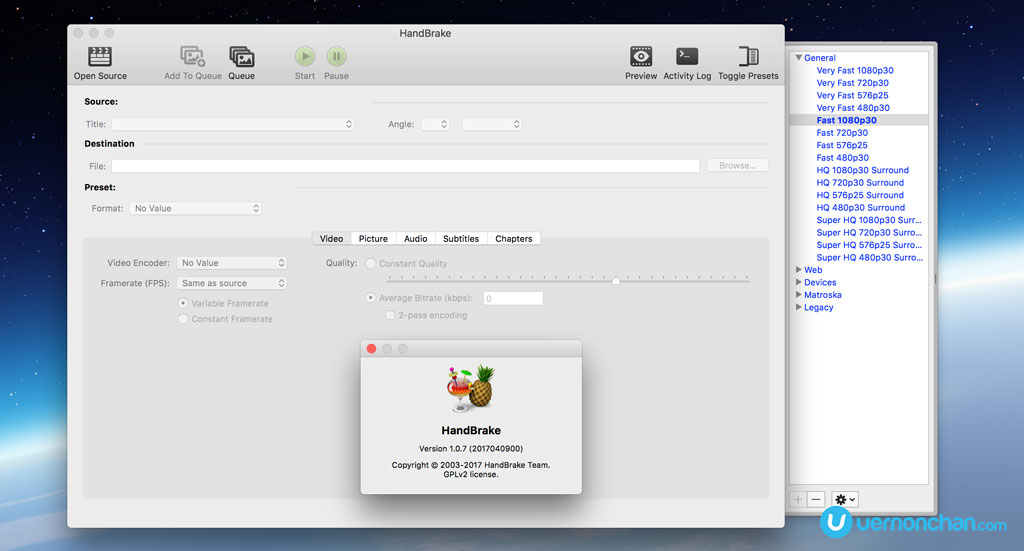
Mac users, take note. The developers of popular open source video transcoder app Handbrake have issued a security warning after one of their mirror download servers was hacked.
An alert was issued on Saturday after the developers discovered that the original Handbrake-1.0.7 dmg installer on the download.handbrake.fr mirror server was replaced by a malicious file. The affected server has been shut down for investigation.
Do note that if you’ve downloaded the app between 14:30 UTC, 2 May and 11:00 UTC, 6 May, there’s a 50% chance that it may be infected by a Trojan. In an alert sent out on Saturday, it warns that if you see a process called “Activity_agent” in the OSX Activity Monitor, then you’re infected.
If you’re infected, here’s how you remove it. You’ll need to fire up Terminal and follow the commands below:
- launchctl unload ~/Library/LaunchAgents/fr.handbrake.activity_agent.plist
- rm -rf ~/Library/RenderFiles/activity_agent.app
- if ~/Library/VideoFrameworks/ contains proton.zip, remove the folder
For reference, if you’ve installed a HandBrake.dmg with the following checksums, you will also be infected:
SHA1: 0935a43ca90c6c419a49e4f8f1d75e68cd70b274
SHA256: 013623e5e50449bbdf6943549d8224a122aa6c42bd3300a1bd2b743b01ae6793
You should remove any Handbrake.app installs from your computer. If you’ve a utility like CleanMyMac, even better.
Just as a precaution, change all your passwords that may be in your OSX KeyChain, or any stored browser passwords.
As a primer, the malware is a new variant of OSX.PROTON – a Mac-based remote access Trojan. It gives the attacker root-access privileges.
In February, Apple updated its built-in security software XProtect to defend against the original Proton. Apple is said to have updated XProtect definitions and it should already be seeded to devices automatically.
According to Handbrake, the Download Mirror Server is undergoing a complete rebuild from scratch, so downloads may be slower than usual.