Ransomware is one of the most widespread and damaging threats facing Internet users today as it scrambles files and renames them, prompting users to buy a decryption key at an exorbitant price.
A recent research by SophosLabs indicates a growing trend among cybercriminals to target and even filter out specific countries when designing ransomware and other malicious cyberattacks. SophosLabs has also seen trends of different ransomware strains that target specific locations, which mean cyber threats can contain vernacular languages, local brands, logos and payment methods, making ransomware highly believable and effective.
Latest technique adopted by cybercriminals
Hackers have turned to injecting JavaScript to spread malware through the web. JavaScript can easily infect websites because it’s a programming language that underpins today’s web. It is primarily implemented as part of a web browser in order to provide enhanced user interfaces and dynamic websites. With today’s Web 2.0 functionality, browsing the web without JavaScript support is no longer a realistic option and Malware authors take advantage of this fact.
Cybercriminals target popular, high-traffic, legitimate websites and redirect users to malicious web pages without the victim’s knowledge. This kick starts the infection process, which results in further exploitation when users visit these malicious sites.
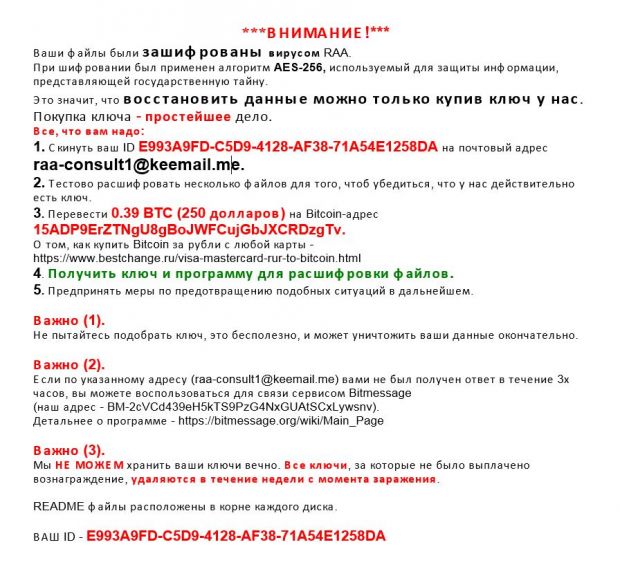
In fact, the latest JavaScript strain known as “RAA”, is ransomware written completely in pure JavaScript, which means the JavaScript does not download the ransomware, it is the ransomware.
The RAA ransomware has recently been circulating through email attachments masquerading as Word.doc files called Invoice.txt.js, which appears as “invoice.txt” on most Windows systems.
Opening the attachment kicks off a series of steps such as scrambling and locking the victim’s files, and downloading and saving additional malware onto the computer. When the victim is distracted paying the ransom, the newly downloaded ransomware launches a password stealing Trojan as the user is likely to begin logging onto sensitive sites to turn some cash into bitcoins; a form of digital currency created and held electronically.
The RAA ransomware adopts a technique that is simpler than the most common method of infection, which involves the use of a Word document containing a malicious macro and attached to an email.
Improving security
IT teams need to understand that traditional security solutions are no longer effective in protecting against unknown variants of ransomware viruses. Signature-based methods to detect ransomware are simply unable to keep up.
In order for threats to be detected and remediated immediately, the network and endpoint should communicate in real-time while being synchronised across the entire threat surface. Sophos refers to this approach as “synchronised security”, as it is an integrated, highly automated security system that is advanced, intelligent and suitable for businesses of any size.
Defending against RAA
Users are encouraged to configure their Windows settings to display file extensions at all times in order to be vigilant against RAA. This measure provides users with a higher chance of identifying suspicious files due to the file type.
If the need to open a JavaScript file arises, users can set Notepad as the default program so the file will be opened as text instead of as a program that runs in the background.

Best practices against ransomware
With ransomware attacks on the rise, the following best practices are recommended to protect organisations:
- Backup files regularly and keep a recent backup copy off-site. Encrypt the backup for an additional layer of protection.
- Do not enable macros to open attachments that are sent via email, as this is how infections are spread.
- Be cautious about unsolicited attachments and refrain from opening it.
- Do not stay logged in as an administrator longer than required, and avoid browsing and opening documents while logged in.
- Consider installing the Microsoft Office Viewer, as the application provides a preview of the document without opening them.
- Patch early and patch often. Any ransomware that is not spread via document macros, often rely on security bugs in popular applications such as Office and Flash.
- Train and retrain employees to avoid booby-trapped documents and malicious emails.
- Separate functional areas within the company network with a firewall so that systems and services can be accessed only if necessary.
Justin Peters is Technology Solutions Director, APAC, Sophos.
Header photo credit: BBC